Secure your Containers hosted on Linux based Azure IAAS Infrastructure
With the rising trend of working with Microservice architecture and DevOps, docker and containers are becoming the best choice for the IT companies to deploy and run their workloads. Although most of the companies are not using the containers for their production environment but its changing with time as the companies are tend to believe in the agility of the containerized environments and it’s robustness.
One of the biggest challenges of going with containers is the security. According to stackrox study about security on containers, only 10% of the companies have advanced security implemented for containers whereas around 37% says that security implementation for containers is not there or it’s too week to handle an attack.
Most of the vulnerabilities happens due to the misconfigurations as the cluster management practice has not matured in lot of IT organizations. One of the bigger issues is companies are not sure what kind of monitoring solutions to use, Implementing Splunk or other SIEMS comes with its own overhead of setting up the infrastructure for it.
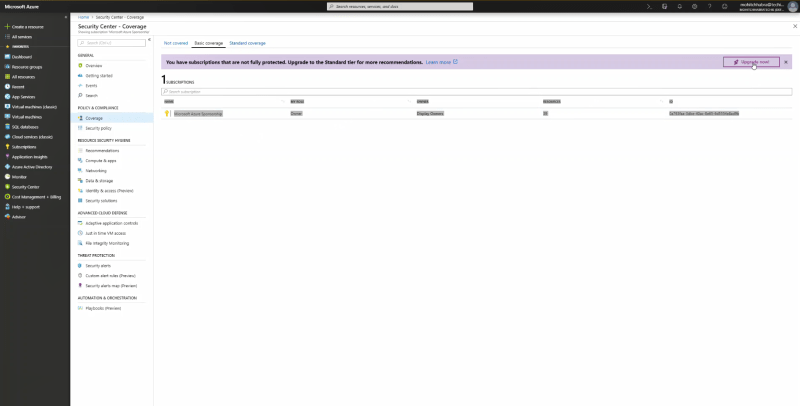
Microsoft has introduced the capability to monitor the containers running on Linux IAAS solutions recently and it seems to work out of the box with Azure Security Center. It requires you to activate your standard license for security center and which is free for two months trial, but you will be charged afterwards so make sure that you read the pricing properly before upgrading to standard tier. Go to Security Center Settings à Select Coverage and Click on Upgrade now to upgrade your subscription.
The service is still in preview so might face some issues using it. I had to wait for a day for my containers to show up in the security center container tab. But once it does, it worked like a charm.
In order to deploy a linux based VM with containers running on it, you can follow my article on it. Once you’re done with the deployment of VM and docker, follow the following steps :
- Go to portal.azure.com and then Security Center. Go to Resource Security Hygiene -> Compute & Apps ->Containers Tab

- The VM that’s running my workload for container is myDockerVM which I deployed in my previous article. I can see that it has 1 recommendation for me and the status is a big RED. Let me click on the VM to see the details.It gives me a list of recommendation and various Informative details about my container. Click on the recommendation to get the details out of it.

- It gives us the details that they have find the vulnerabilities in our container. Microsoft has run through their KB of security rules and found that it’s violating some of the rules. In this particular case, we have 3 threats of Data Exfiltration, Data spillage and even even account breach. From the security point of view, all there are big security threats and should be fixed asap and I had no idea of these threats before using security center. Click on Take Action Button to start fixing the issues.

- It will take you to the log analytics and you can find all the rules that are failing in your configuration. As I mentioned above, most of the attacks or breach happens in a containerized environment because of the misconfigurations or not the best configurations in the cluster. I too got the same issue pointed by the security center.

Summary
Microsoft Security Center gives you the capability to scan and audit your container cluster. It runs through the best practices and security rules and give the recommendation based on that. Once you Identify them, fix them to be secured.